Secret Detection in Code: A Complete Guide for 2026
According to GitGuardian's State of Secrets Sprawl 2025 report, over 23.7 million hardcoded secrets were pushed to public GitHub repositories in 2024, a 25% increase over the previous year. API keys, database passwords, OAuth tokens, and private certificates are leaking into source code at an accelerating rate. Worse, 70% of those exposed credentials remain active more than two years later. Secret detection in code is the automated process of scanning source code, configuration files, and version control history for these exposed secrets before malicious actors find them first. This guide covers why secrets leak, how secret detection tools work, which tools to evaluate, and how to build a security strategy that scales across enterprise environments.
What Is Secret Detection in Code?
Secret detection is the practice of running automated scans to identify hardcoded credentials embedded in source code and version control history. API keys, database credentials, access tokens, encryption keys, SSH private keys, service account passwords: any string that grants programmatic access to a system qualifies as a "secret" in this context.
The core problem is straightforward. Developers need credentials to build and test software. Under deadline pressure, those credentials get hardcoded into configuration files or application code. Once committed to a Git repository, the secret persists in the commit history even after the line is deleted from the current branch. Manual code review catches some of these mistakes, but not consistently and not at scale. Secret detection tools automate this process by scanning code for patterns that match known credential formats, flagging potential secrets before they reach production environments.
For organizations managing hundreds or thousands of source code repositories, the challenge goes beyond catching new secrets at commit time. Teams also need to search their entire existing codebase for credentials committed months or years ago. Sourcegraph's Code Search addresses this gap by enabling regex and structural pattern matching across every repository and code host in an organization, surfacing hardcoded secrets that pre-commit scanners never had the chance to catch.
Why Secrets Get Exposed in Source Code
The root causes are rarely malicious. They are almost always a byproduct of how modern development workflows operate across the software development lifecycle.
Development velocity outpaces security hygiene. A developer needs a database connection string to test locally, pastes it into a config file, gets the feature working, and ends up pushing secrets to the remote. The intent was always to remove it later, but "later" never comes. The secret sits in the commit history permanently.
Copy-paste from documentation is widespread. Cloud services quickstart guides often include example credentials or encourage users to export keys as environment variables. According to the OWASP Secrets Management Cheat Sheet, hardcoding credentials in configuration files and source code is among the most common causes of secret leakage.
AI coding assistants introduce new risk. GitGuardian's State of Secrets Sprawl 2025 report found a 6.4% secret leakage rate in repositories using GitHub Copilot, higher than baseline repositories. Code generation tools suggest patterns that include placeholder credentials, and developers who accept suggestions without review inadvertently commit sensitive credentials.
Secrets spread beyond code repositories. The same report found that 6.1% of Jira tickets and 2.4% of corporate Slack channels contained leaked credentials. Developers share connection strings in chat, paste tokens into issue descriptions, and embed credentials in CI/CD configuration files. This sprawl of sensitive information makes centralized secrets detection harder.
Multi-repo architectures amplify the problem. When an organization manages hundreds of repositories across multiple code hosts, a single leaked credential can be duplicated across dozens of projects and development environments. Sourcegraph's universal code search handles this by indexing code from GitHub, GitLab, Bitbucket, and other hosts into a single searchable interface, so teams can run a regex query once and find every matching pattern across their entire codebase.
Common Types of Secrets Found in Codebases
Not all secrets carry the same risk. Understanding the categories helps developers and security teams prioritize detection rules and remediation efforts.
Cloud provider credentials are among the most dangerous. AWS access keys (identifiable by the AKIA prefix), Google Cloud service account JSON files, and Azure connection strings grant direct access to infrastructure. GitGuardian's 2025 report found that 96% of exposed GitHub tokens had write access, potentially leading to unauthorized operations, including code injection and supply chain compromise.
Database connection strings contain the hostname, port, username, and password in a single URI. A leaked Postgres string like postgresql://admin:p4ssw0rd@db.example.com:5432/production gives an attacker direct read/write access to sensitive data, including customer data.
API keys and tokens range from low-risk (read-only public API keys) to critical (payment processor keys like Stripe secret keys, which start with sk_live_). Private keys and certificates include SSH private keys (-----BEGIN RSA PRIVATE KEY-----), TLS certificates, and signing keys. These are multi-line secrets that some code scanning tools miss because they look for single-line patterns.
Internal service credentials are the hardest to detect: internal API tokens, service mesh authentication credentials, and microservice-to-microservice keys follow no public format, so organizations need custom detectors with tailored detection rules.
Teams using Sourcegraph can search for these patterns across their entire codebase using regex queries. For example, searching for AKIA[0-9A-Z]{16} patterntype:regexp across all indexed repositories returns every file containing a potential AWS access key, across all git repositories and code hosts in the organization.
Risks of Hardcoded Secrets in Applications
The business impact of secret exposure extends far beyond the immediate credential compromise, often resulting in data breaches and serious security issues.
Financial damage is substantial. According to the IBM Cost of a Data Breach Report, breaches initiated through compromised credentials cost an average of $4.67 million. These breaches take 246 days to identify and contain, the longest timeline of any attack vector.
Supply chain attacks escalate the blast radius. A leaked GitHub token with write access can inject malicious code into dependencies consumed by thousands of downstream projects. With 96% of exposed GitHub tokens granting write access, the supply chain risk from a single leaked credential is significant.
Regulatory consequences add to the cost. PCI DSS, SOC 2, and HIPAA all require organizations to protect credentials. The OWASP Non-Human Identities Top 10 ranks secret leakage as one of the most common security vulnerabilities, noting that 31% of NHI-related security incidents stem from poorly managing secrets and access control.
Remediation at scale is operationally expensive. When a secret is discovered in one repository, teams need to find every instance across other projects, CI/CD configurations, container images, and documentation. Sourcegraph's Code Search enables teams to run a single query across all repositories and code hosts to find every instance, reducing investigation time from days to minutes. Batch Changes then automates opening pull requests to rotate or remove secrets across hundreds of repositories simultaneously.
How Secret Detection Tools Work
Secret detection tools use a combination of techniques to identify credentials in source code. Each detection engine has strengths and trade-offs that affect accuracy, coverage, and performance.

Pattern matching with regular expressions is the foundation of most detection tools. Each known secret type has a predictable format: AWS access keys start with AKIA, GitHub tokens start with ghp_, Stripe live keys start with sk_live_. Detection tools maintain libraries of regex patterns and scan code for matches. GitGuardian maintains over 450 specific detectors, while TruffleHog covers more than 800 secret types. This approach has high precision for known formats, but cannot detect secrets that follow no standard pattern.
Entropy analysis complements pattern matching by detecting high-randomness strings. Entropy-based scanners flag strings that exceed a randomness threshold, catching potential secrets that no regex would match. The trade-off is a higher false positive rate: base64-encoded data, UUIDs, and hash values also have high entropy. Tools like detect-secrets combine entropy analysis with keyword detection (flagging variables named password, secret, or api_key) to reduce noise.
Machine learning models add contextual awareness. ML-based detectors analyze surrounding code to determine whether a flagged string is a real credential or a test fixture. GitGuardian reports 85-95% precision from their ML-powered generic secret detection, effective for the 58% of leaked secrets that are generic rather than format-specific, providing actionable insights that help security teams prioritize remediation.
Credential verification is the most definitive technique. After identifying a potential AWS key, TruffleHog calls the AWS GetCallerIdentity API to confirm whether the credential is actually valid, eliminating false positives entirely for verified secrets.
Where Sourcegraph fits in this workflow: dedicated scanners monitor new commits for secrets. But a scanner installed today will not flag the AWS key committed eighteen months ago. Sourcegraph's regex and structural search capabilities let teams query their entire code history for credential patterns, finding the secrets that pre-commit hooks never had the chance to catch. Combined with Code Insights, teams can track over time how many repositories still contain matches to specific secret patterns.
Static vs Dynamic Secret Detection Methods
Secret detection strategies fall into two categories based on when and where they run. A comprehensive protection strategy combines both across the development lifecycle.
Static detection scans code at rest: files on disk, committed code in repositories, and container image layers. This category includes pre-commit hooks, CI/CD pipeline scanners, and repository-wide audits. Static detection is predictable, fast, and does not require the application to be running.
Pre-commit hooks run on the developer's machine before code reaches the repository. Integrating secrets detection at this stage, tools like Gitleaks and GitGuardian's ggshield work as Git hooks that reject commits containing detected secrets. The limitation: pre-commit hooks can be bypassed with --no-verify, and they only protect repositories where they are explicitly configured.
CI/CD pipeline scanning catches secrets that bypass pre-commit hooks. GitHub's built-in secret scanning (which generates secret scanning alerts to notify developers) and GitLab's pipeline secret detection operate at this layer. Enforcement is stronger because pipeline policies cannot be bypassed locally.
Repository-wide scanning audits the entire codebase and its Git history. TruffleHog and Gitleaks (in full-history mode) scan every commit ever made to find secrets that were committed and later deleted. For organizations with hundreds of repositories, running individual scans is operationally complex. Sourcegraph provides deep integration as a centralized search interface across all code hosts, letting security teams run a single regex query across the entire organization in seconds.
Dynamic detection monitors running systems and runtime configurations for exposed credentials, including cloud environment variables, Kubernetes secrets, and API traffic. Dynamic detection catches secrets that static analysis misses but operates later in the lifecycle, after the secret is already deployed.
The OWASP DevSecOps Guideline recommends combining pre-commit, server-side, CI/CD, and runtime scanning as a defense-in-depth strategy.

No single layer catches everything, which is why continuous integration of security measures across all stages strengthens an organization's overall security posture. Pre-commit hooks are the fastest feedback loop but the easiest to bypass. Runtime monitoring is the hardest to bypass but provides the slowest feedback.
Popular Secret Detection Tools for Developers
Choosing the right secret detection tool depends on your code hosting platform, organization size, existing infrastructure, and whether you need to scan existing codebases or prevent secrets from entering new code.
Gitleaks is the most widely adopted open-source scanner. Written in Go as a single binary, it supports over 160 secret types and scans both current code and full Git history. With 19,000+ GitHub stars and 20 million Docker downloads, it is the best starting point for teams that want a no-cost, no-dependency scanner.
TruffleHog differentiates itself through credential verification. Beyond regex and entropy detection across 800+ secret types, TruffleHog validates discovered credentials against service APIs to confirm they are actually active. With 23,000+ GitHub stars and 250,000+ daily runs, the enterprise version extends scanning to Slack, Jira, Confluence, and other collaboration tools.
detect-secrets (by Yelp) takes a baseline-first approach designed for legacy codebases. Rather than flagging every historical secret, it creates a baseline of known secrets and only alerts on new ones, making it effective for brownfield projects. It uses 27 built-in detectors and offers a Python plugin API for custom rules.
GitGuardian is the most comprehensive commercial solution, with 450+ specific detectors and ML-powered generic detection, achieving 85-95% precision. Its open-source ggshield CLI works as a pre-commit hook and CI/CD integration, excelling at multi-line secrets and multi-match patterns that simpler tools miss.
GitHub Secret Scanning requires no setup for public repositories. It notifies service providers when their credentials are detected, enabling automatic revocation. Push protection prevents commits containing detected secrets from being pushed. The limitation: approximately 50+ secret types and GitHub-hosted repositories only.
GitLab Secret Detection provides native pipeline-based scanning with 100+ default patterns and client-side detection in issues and merge request descriptions, catching secrets before they reach the repository.
What these tools do not cover is equally important. Every tool in this table focuses on detecting secrets by scanning new commits or auditing history. Most do not provide interactive search across an entire organization's codebase or track remediation progress as a measurable metric. This is where Sourcegraph complements dedicated scanners.
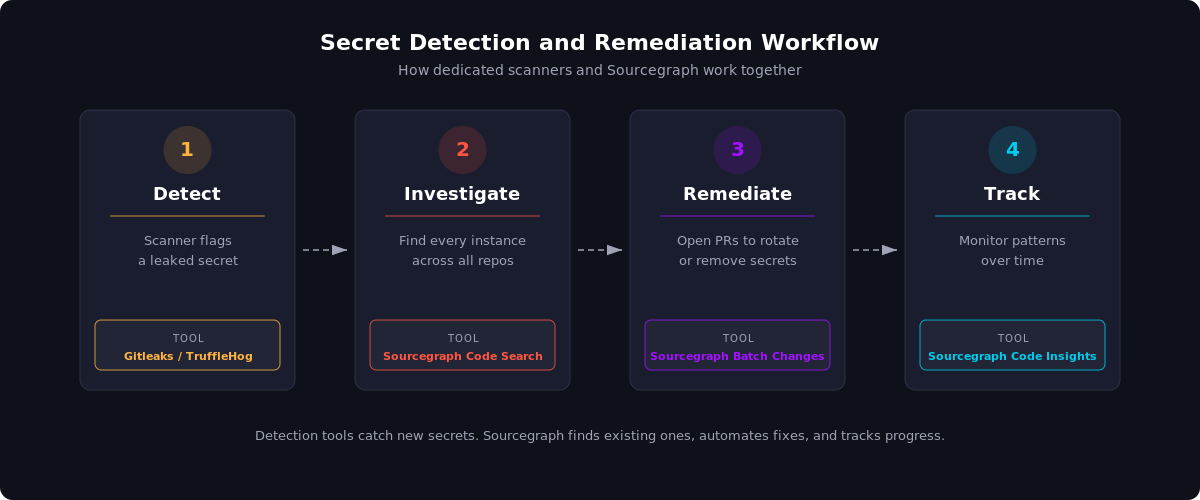
After a detection tool flags a leaked AWS key, a security team can use Sourcegraph to find every instance across all repositories and use Batch Changes to open remediation PRs simultaneously. Code Insights then tracks matches over time, turning secret remediation from a one-time audit into an ongoing process with actionable insights into your organization's security posture.
Conclusion
Secret detection is a necessary layer of code security, but it is not sufficient on its own. Pre-commit hooks stop new leaks, CI/CD scanners enforce policy, and repository auditors surface historical exposure. Together with secure practices like secret rotation and encrypted data at rest, they form the detection layer of a complete secrets management strategy. The key takeaways: no single tool is enough, and managing secrets effectively requires layered security measures across the entire development lifecycle.
The harder problem is what comes after detection: finding every instance of a credential across all repositories, determining which services it grants access to, rotating it, and verifying the rotation did not break anything. At enterprise scale, this investigation-and-remediation workflow across all source code repositories is where most organizations struggle.
Sourcegraph's Code Search lets security teams search across every repository and code host for credential patterns in seconds. Batch Changes automates remediation by opening pull requests across affected repositories. And Code Insights tracks secret pattern matches over time, giving security leaders visibility into whether remediation is actually working.
Start by deploying a scanner like Gitleaks or TruffleHog to keep your code secure and block new leaks, then use Sourcegraph to audit your existing codebase and public repository history for exposed credentials that have been hiding in plain text for months or years.
.avif)

